|
Security features deter unauthorized use of your system and data. If you use
your server in a public environment, such as an office, you might want to
protect it and the data stored on it, by using one or more security features.
Before implementing any security features, you might begin by evaluating your
security needs. Where will the system be located? Does it need to be secured to
permanent furniture or fixtures? Should use of the system be limited? When you
have identified your security needs, you can activate or implement the
appropriate security features.
LogicLock (comes with SurePath systems)
Securing Hardware
U-Bolt Facility
Door Locks and Keys
Cable Cover Option
Unauthorized-Access Monitor (Includes ServerGuard)
Removable Media
Securing Data
Power-On Password
Unattended Start Mode
Administrator Password
Keyboard Password
Selectable Drive Startup
Secure IPL Source
Securing Data from Loss
Backup Copies
Redundant Copies
Parity Information
Viruses
Erased Files
Backup Power Supply
Uninterruptible Power Supplies
Standby Power Supplies
LogicLock (Comes with SurePath systems)
Note:
We are not sure on how the LogicLock switches provide
input to the CMOS. At this point, I am not sure if
there are ancillary ICs involved with storing status
outside of the CMOS. So until further notice, don't
enable the PAP (Unauthorized Access Monitor).
LogicLock (advanced security features) that come with
your server include tamper-evident switches. This active
security feature
uses microswitches on the covers to indicate if someone
has tried to open
the front cover. Location and pinout of Cover Interlock
Connector (JMP3).
If the case cover is forced while PAP is enabled, the
CMOS user configuration will be erased and the system
power will be shut off. This will force an
autoconfiguration or manual configuration, but either
will require the use of the Administrator or Privileged
Access Password (PAP).
Note: If the PAP
is forgotten, the planar must be replaced or returned
for repair.
Extended Control Register A (Hex 4A)
Bit 2 - "TF" tamper-evident status bit shows if cover
breached, clearing CMOS and generating an interrupt.
Setting this bit to "0" clears the interrupt. (the
clear-RAM enable bit must be set to "1" for this status
bit to be set to "1")
Extended Control Register B (Hex 4B)
Bit 4 - "CLR" the clear RAM enable bit controls the
tamper evident logic. When set to "1", config info in
CMOS RAM is erased when cover breached. When this is "0"
CMOS RAM is not erased.
Bit 2 - "TE" tamper evident interrupt enable bit
determines if interrupt is generated if covers breached.
When "1" an interrupt is generated after CMOS cleared.
Michal Necasek said
These are equivalents of what the Dallas datasheet
says. Bit 2 in register 4Ah is actually the ‘RC’ or RAM
clear flag indicating that the RAM was externally
cleared. Bit 2 in register 4Bh is ‘RIE’ or RAM clear
interrupt enable, triggering an interrupt via a RAM
clear event. Bit 4 is ‘RCE’ or RAM clear enable.
So yes, the tamper-evident functionality was
directly mapped to the RAM clear circuits of the Dallas
chip.
Pinout of the Cover Interlock Connector (JMP3) can be found
HERE.
Notes:
1. When cover is removed, power is
removed from computer.
2. For 00014908 or 00014909 while
testing system with front bezel installed, do
this:
1.Remove side
cover.
2.Install front bezel.
3.While observing SW1 (on side
of drive support
structure), operate keylock.
4.If operating keylock does
not fully operate SW1,
replace keylock assembly and switch transfer assembly
located
inside front bezel.
|
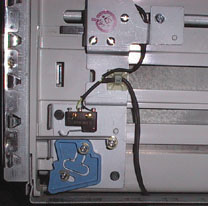
The lower lever switch (above blue cam assembly)
passes through
a cutout to engage a plastic lever arrangement on the
front of the drive
retainer. When the lock is in the engaged position, the
end of the locking
tab goes up, closing the microswitch.
The upper assembly has a plunger sticking out of
the front side.
That plunger is actuated by a long post that is part of
the front case cover.
|
Securing Hardware
One of the best methods for protecting your
hardware from
theft is to keep it under lock and key. One method of
deterring theft is
to fasten the hardware to a stationary object, such as a
table, a desk,
or a wall. Another approach is to locate critical
resources, such
as servers, in a limited-access area behind locked
doors.
The security features of your server
include the U-bolt
facility, which allows you to secure the system to a
stationary object
with a cable or chain. It also includes the door
lock and keys.
Subtopics:
o U-Bolt Facility
o Door Locks and Keys
o Cable Cover Option
o Unauthorized-Access
Monitor
U-Bolt
Facility
If your server is in an area that is
accessible to the
public, you might need a method of securing it to a
desk, table, or other
stationary object. Two holes are provided at the
rear of the server
to accommodate a U-bolt. After the U-bolt is
installed (See Installing a
U-Bolt), you can use a cable or chain to
lock the server in
place. (This capability is referred to as a
cable-down or a bolt-down
feature.)
Door Locks
and Keys
There is one door lock which mechanically
deters access
to the drives. It controls access to the small
door that covers the
removable media drives as well as the entire front
cover. If the covers
are forced open without unlocking the lock, a
microswitch detects the intrusion.
The next time the system is started, the power-on
self-test displays a
message informing you that the covers have been tampered
with, and that
you must run the Automatic Configuration program before
you can use the
system.
Two keys are provided with your
server. Always store
the keys in a safe place. If you lose them, you
must order a replacement
lock mechanism and keys from IBM. Please note that
anyone who has
the key serial number and manufacturer's address can
order duplicate keys,
so store the tag in a safe place.
Cable
Cover Option
The cable-cover option prevents the cables
from being
removed from the rear of the server, and prohibits other
computers or devices
from being attached to the unused connectors.
Note: The
cable cover does
not protect against unauthorized access through devices
attached outside
of the system.
Unauthorized-Access
Monitor
The unauthorized-access monitor feature
works with the
administrator (also known as privileged-access)
password, when you are
using DOS. If you set an administrator password
and the unauthorized-access
monitor feature is enabled, your server will alert you
if an attempt has
been made to tamper with the locked covers. (If
you have a ServerGuard
attached, it will dial out or send a message on the LAN)
If it detects
any tampering, the system will stop all operations or
display an error
message. If the system stops, any data in memory
waiting to be stored
might be lost. (The response to tampering varies
with the operating
system you are using.)
When you set an administrator password,
the unauthorized-access
monitor is automatically enabled. If you do not
want the system to
stop operations if the covers are tampered with, set the
unauthorized-access
monitor to Disable. You can change the setting of
this feature through
the Change Configuration screen.
Removable
Media
If you are using your server in an
environment where a
diskette is left in the drive while the server is
unattended, an electronic-eject
diskette drive can provide the security you need to
protect the diskette
from theft or damage. This separately purchasable
diskette drive
allows you to lock a diskette in the drive or prohibit
someone from inserting
a diskette in the drive, while the drive is not in
use. However,
the operating system you are using must provide a means
of activating this
feature (such as entering a password).
Not all operating systems support this
feature.
Securing
Data
It is very difficult to secure shared
information from
theft, but an effective method is to limit user
access. Only users
who need the software or data should be able to access
it. This level
of access control is provided as a standard feature of
most network programs.
Another common feature of network programs that helps
secure data from
theft is password protection. Passwords are easy
to use and very
effective. They help prevent unauthorized users
from accessing sensitive
files.
Some advanced network management programs
can actually
audit usage, based on names, adapter addresses, date,
time, and unsuccessful
attempts to access a file. This type of
information can help you
identify users who are attempting to access restricted
data.
To secure extremely sensitive data, you
might want to
consider using a commercially available data-encryption
tool. These
tools encode the data files so that they are
unintelligible, thus useless
if stolen. There are two ways that you can encrypt
data: by using
a program or using an encryption device. The
software programs are
usually less expensive than the hardware devices, but
they also are slower.
Subtopics:
o Power-On Password
o Unattended Start
Mode
o Administrator
Password
o Keyboard Password
o Selectable Drive
Startup
o Secure
IPL Source
Power-On Password
You do not need to use a power-on password
to use your
server, but a password helps protect the information you
store in it.
You can use any combination of up to seven characters
(A-Z, a-z, and 0-9)
for your power-on password. Keep a record of your
password in a secure
place. If you forget it, you will have to remove
the server cover
and change the position of a specific
jumper to erase it.
The power-on password locks the keyboard
and mouse (if
attached to the mouse port) to help prevent unauthorized
use of your server.
If you are using a mouse that is connected to the serial
port, the mouse
remains active.
After you set a power-on password, Enter
password appears
each time you turn on the server. Before you can
use the server,
you must enter the correct password. (The password
does not appear
on the screen as you type it.) When you enter the
correct password,
Password accepted appears on the screen, the keyboard
and mouse are unlocked,
and the system resumes normal operation. If you
type the wrong password,
Incorrect password appears on the screen and Enter
password is again displayed.
After three incorrect attempts, you must turn off the
server and start
again.
Unattended
Start Mode
After you set a power-on password, you can
enable the
unattended start mode. This mode locks the
keyboard and mouse, but
allows the system to start the operating system and
carry out the instructions
in the CONFIG.SYS and AUTOEXEC.BAT files.
Although Enter password does not appear,
the keyboard
and mouse remain locked until you enter the correct
password. This
mode is ideal for systems that operate unattended.
If a power failure
occurs, the system automatically restarts when power
returns and resumes
normal operation, without operator intervention.
ATTENTION MOUSE USERS:
The
following statement applies only to those who use a
PS/2-style mouse;
a serial mouse is not affected.
In the unattended start mode, the keyboard and mouse
ports are disabled
(locked). Because of this, the system cannot
detect that a mouse
is attached, and an error occurs.
You must do one of the following:
o In the
CONFIG.SYS file,
set the operating system so that it does not stop on a
device-driver error.
For example, under OS/2 , use the PAUSEONERROR=NO
statement.
o Remove
mouse driver statement
from CONFIG.SYS file if you do not want to use a
mouse.
When using the OS/2 operating system, if
you do not perform
one of the previous steps, the system issues an error
message, halts, and
prompts you to press Enter to continue. Before
pressing Enter, type
the power-on password.
Refer to your operating-system
documentation for information
about modifying your CONFIG.SYS and AUTOEXEC.BAT
files.
Administrator
Password
Before setting an administrator (also known
as privileged-access)
password, it is a good idea to read this section in its
entirety.
Using this security feature requires some planning and
ongoing administration.
The administrator password allows you to
control who has
access to the system programs. If an administrator
password is set,
you must enter it to use the system programs in the
System Partition on
the hard disk or on the Reference Diskette. The
administrator password
also can be used to override the power-on
password. After an administrator
password is set, only those who know the password can
perform tasks such
as:
o Altering computer settings or features controlled by
the system programs
o Running diagnostic tests
o Resetting the system after a forced entry (If the
server is forced
open, a POST error occurs. To clear the error, you
must enter the
administrator password.)
Your server is shipped with the administrator
password feature
Disabled. You must move a jumper
on the system board before an administrator password can
be set for the
first time. The jumper has two positions:
o Locked state - prevents administrator password from
being set,
changed, or removed. This is the position set at
the factory.
o Change state - allows an administrator password to be
set, changed,
or removed.
Warning! If an
administrator password
is set, then forgotten, it cannot be overridden or
removed. The system
board must be replaced in order to access the system
programs.
Subtopics:
o How the
Administrator
Password Works
o Setting an
Administrator
Password
o Forgotten
Administrator
Password
How
the Administrator Password Works
Use the administrator password when highly
classified
information must be protected. Although it can be
used with your
power-on password, it provides a much higher level of
security when used
with an operating system that controls access through
the use of passwords.
This type of operating system is called a secured or
trusted computing
base.
You can use any combination of up to seven
characters
(A-Z, a-z, and 0-9) for your administrator password,
just as you can with
your power-on password. For additional security,
the two passwords
should not be the same.
One important difference between the
power-on password
and the administrator password is that a forgotten
administrator password
cannot be overridden or disabled. The single most
important reason
for setting an administrator password is that when one
is set, only those
who know the password can access the system programs and
modify the hardware
or change any of the settings.
If you type the wrong password, Incorrect
password appears
and Enter the privileged-access password is again
displayed. After
three incorrect attempts, The system is locked message
is displayed and
you must turn off the server and start again.
Setting
an Administrator Password
In order to set an administrator password,
you must first
set your selectable drive-startup sequence. (If
you try to set this
password and the drive sequence is not set, an error
code and text message
with instructions appear.) You can select the
default drive-startup
sequence, which includes a diskette drive. To have
a totally secure
system, you can remove the diskette drive from the
drive-startup sequence.
Forgotten
Administrator Password
If an administrator password is set, then
forgotten, it cannot
be overridden or removed. If you forget your
administrator password,
you must replace the system board to gain access to the
system programs.
Keyboard Password
A keyboard password allows you to lock the
keyboard while
the system is turned on. This is useful if you
leave your system
on and unattended. With the keyboard locked, no
one can use or restart
your system.
The way you set the keyboard password
depends on the operating
system you are using. The OS/2 operating system
provides keyboard-password
protection as a standard feature.
If you forget your keyboard password, turn
off the server
for at least 5 seconds; then turn it on. The
keyboard password is
erased from memory when you turn off the server.
Selectable
Drive Startup
Selectable drive startup (sometimes
referred to as selectable
boot) allows you to control the startup sequence of the
drives in your
server. Each time you turn on the server, it
checks the drives as
it looks for the operating system. The order in
which the system
checks the drives is the drive-startup sequence.
In most cases, you do not need to change
the default drive-startup
sequence. However, if you set an administrator
password, or are working
with multiple hard disk drives, multiple operating
systems, or different
sized diskette drives, you might want to change the
default drive-startup
sequence.
The default drive-startup sequence checks
the primary
diskette drive for a self-starting (bootable)
diskette. If one is
present, the operating system or program is loaded from
the diskette.
If not, the system checks the primary hard disk for an
operating system.
If one is present, it is loaded from that hard
disk.
If you start the system from a diskette,
the drive containing
the diskette becomes drive A, regardless of the defined
sequence, and the
first hard disk selected in the startup sequence becomes
drive C.
You can choose a startup sequence of up to four
drives.
You can customize the startup sequence by
changing the
order in which the system checks the drives. You
decide which four
drives are the first to be checked, and the order in
which the system checks
them.
Notes:
1. If a Reference Diskette is present in a
diskette drive that
is not in the selectable boot sequence, POST will boot
that diskette only
if you press F1 or (Alt+Ctrl+Ins) at the server
startup.
2. When you change the startup sequence, the
drive letters also
might change. The operating system assigns the
drive letters when
the system starts. Letters A and B always are
assigned to diskette
drives. Subsequent drive letters can be assigned
to any type of drive based on the operating system or the
device drivers used.
Warning! If you
changed your startup
sequence, you must be extremely careful when doing write
operations (for
example, copying, saving, or formatting). You can
accidentally overwrite
data or programs if you select the wrong drive.
Secure IPL
Source
The Server 95 allows the system owner or
administrator
to control the IPL source by specifying the startup
sequence (see Selectable
Startup Sequence). With the privileged-access password
active, the system
owner can control the IPL source by excluding the
diskette drives from
the startup sequence; the password prevents anyone from
modifying the source
and sequence.
The setup routine ensures that at least
one source is
specified if the privileged-access password is
used.
Earlier PS/2 models could also specify the
startup sequence;
however, the sequence was stored in CMOS and could be
erased. In
these systems, the sequence is stored in nonvolatile
memory and cannot
be deactivated by removing a battery.
Securing
Data from Loss
There are several methods you can use to
prevent the loss
of data. You should consider these methods
carefully, because some
of them affect the performance, reliability, and
hardware requirements
of the server.
There are primarily three ways that you
can protect your
data from loss. You can wait until the data
accumulates on the server,
and then make backup copies of all the hard disks.
You can configure
a disk array to duplicate data (create a redundant copy)
as it is entered,
and then store the duplicate copy on a separate hard
disk. Or, you
can configure a disk array to store the parity
information about the data
on the array as the data is being entered.
Subtopics:
o Backup Copies
o Redundant Copies
o Parity Information
o Viruses
o Erased Files
o Backup Power Supply
Backup
Copies
A good method for preventing the loss of
data is to make
copies of the data. In the event of a hardware
failure you can always
recover using the copies.
Backing up the entire contents of a hard
disk to diskettes
can be very time-consuming and, in the case of a network
server that has
multiple hard disks, might require hundreds of
diskettes. A faster
and more efficient way to back up the data is to use a
tape-backup drive.
Using a tape-backup drive, you can copy several billion
bytes of data from
the hard disks to a single tape.
There are two problems with making backup
copies.
The first problem is someone has to remember to do
it. The second
problem is that you usually need to disconnect the
server from the network
to make the backup copies.
Redundant
Copies
A convenient way to copy the contents of a
hard disk is
to duplicate all data as it is being entered. This
duplicate copy
is then stored on another hard disk. If one hard
disk fails, you
still have access to the data on the other. This
method is more expensive
than backing up to diskettes or tapes, because it
doubles the amount of
disk-storage space needed.
Parity Information
Storing parity information about the data
as the data
is being entered is an efficient, cost effective, and
reliable method commonly
used to guard against the loss of data. In the
event of a hard disk
failure, the parity information and the data on the
remaining functional
disks are used to reconstruct the data that was stored
on the failed drive.
Viruses
Computer viruses are a problem that exists
within the
personal computer community. A computer virus is a
program (or instructions
hidden within a program) that infects other programs by
modifying them
without your knowledge. Like any other program,
the virus can do
anything it is programmed to do. Some viruses are
practical jokes,
causing unusual or erratic screen behavior. Others
are destructive,
erasing or damaging files or overloading memory and
communication networks.
Viruses are difficult to detect.
Many stay inactive
until triggered by a specified event such as a date,
command, or some other
operation. Others are activated when an infected
program is started
a specified number of times. When the symptoms of
thevirus appear,
it might be difficult to determine if the problem is a
hardware failure,
a problem in the software, or a virus in action.
Several programs are available that can
detect the presence
of many known viruses. These programs typically
examine files and
look for patterns associated with these viruses, or look
for changes in
the size of files. These programs are best used as
a preventive measure
to detect a virus before it becomes widespread or causes
damage.
Many computer users check for viruses on a regular
basis.
When a virus is found, it must be
removed. This
might be as simple as replacing a file, or it might
require the assistance
of a trained technician.
Viruses are generally spread unknowingly
from computer
to computer when programs are exchanged or shared.
If you don't know
where a program came from, be careful. Most
reputable program distributors
and bulletin-board owners scan their files to guard
against viruses and
maintain records to identify program owners.
Here are a few tips to help
guard against computer
viruses:
o Write protect original program diskettes before using
them.
This ensures the diskettes will not be infected if a
virus is already present
in your system.
o Avoid using programs and diskettes from unknown
sources.
o If you use programs provided from public-domain
software distributors
or BBSs, find out what precautions they take to guard
against viruses.
o Back up all critical data and programs
regularly.
o Watch out for changes in file sizes (when they
shouldn't change).
o Use password protection to limit access to your system
or network.
Remember, not every problem is caused by a
virus.
If your system starts acting erratically, refer to your
troubleshooting
charts in the User's Handbook to test the system.
Erased
Files
Erasing a file from a diskette or hard disk
does not destroy
the file. With the right type of software, all or
part of an erased
file can be reclaimed. This can cause a security
risk if you sell
a system or give someone a diskette that once contained
classified or confidential
information.
One way to help ensure that no readable
information is
left on a hard disk is to do a low-level format.
An operating-system
format operation does not remove all information from a
hard disk.
The operating-system format operation
works a little differently
with diskettes. It writes a repeated pattern over
the entire surface.
Any information that was on the diskette becomes
unreadable.
Depending on the type of information
stored, you might
require additional safeguards.
Backup
Power Supply
To prevent the loss of data caused by a
power fluctuation,
you might want to consider installing a backup power
supply. There
are two basic types of commercially available backup
power supplies:
uninterruptible and standby.
Subtopics:
o Uninterruptible
Power Supplies
o Standby Power Supplies
Uninterruptible
Power Supplies
This type of power supply works as an
interface between
the main power source and the server, and it
automatically takes over when
the main power source is lost. An uninterruptible
power supply connects
directly to the main power source (electrical outlet),
and then the server
connects to the power supply. The power supply
transfers the power
from the main power source to its internal battery; then
its internal battery
provides the power to the server. The advantages
of uninterruptible
power supplies are that they require no switching time
(because they are
always on), and they protect the server from power
surges. A disadvantage
is that they usually cost more than standby power
supplies.
Personal Experience!
The 9595 power supply DEMANDS sine wave
voltage! Your
UPS MUST supply TRUE sine wave voltage or you WILL
experience random shut
downs, then power-ups of your 9595s power supply. Really
sucks when you're
on-line and your machine shuts down. The UPS will not go
into back-up when
this happens. It's not the UPSs fault.
Standby
Power Supplies
This type of power supply waits until it
detects a drop
in voltage, and then it switches on and provides power
to the server until
its battery power is depleted. An advantage of a
standby power supply
is low cost. It is usually less expensive than an
uninterruptible
power supply. A disadvantage of a standby power
supply is the amount
of time that it needs to switch itself on; the more time
it takes, the
greater the chance of losing data.
|